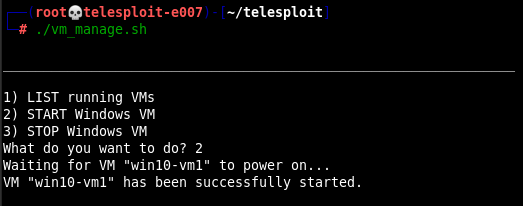
If the Telesploit deployment includes the optional Windows virtual machine then the VM must be launched before connecting to it. From a console connected to the Telesploit server navigate to the /root/telesploit directory and run the script manage_vm.sh.
./manage_vm.sh
Select Option 2 “START Windows VM” and hit return.
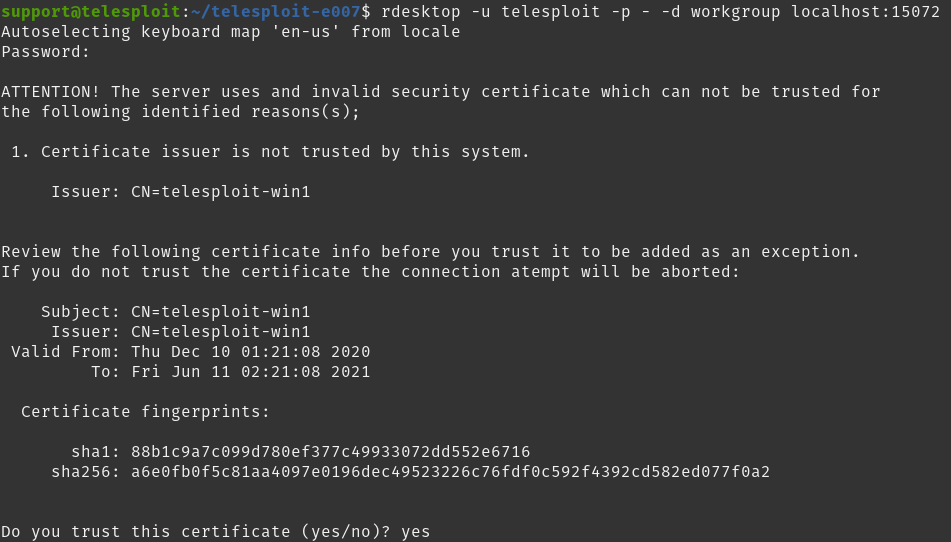
Once tunnels to the relay have been established an RDP client may be used to connect using the following configuration.
Example RDP Configuration
Host: localhost (127.0.0.1)
Username: telesploit
Password: telesploit
Domain: workgroup
Port: Assigned RDP port
The following example uses rdesktop to access the Windows VM.
Example: Connect with rdesktop
rdesktop -u telesploit -p - -d workgroup localhost:15072
NOTE: As this service is only listening on localhost, and connectivity depends on SSH key authentication, the username and password are superfluous and have thus been set to ‘telesploit’ for all deployments.
A successful connection provides desktop access to the Windows VM on the Telesploit server.



