NOTE: Replace all FQDNs and port numbers in the documentation with those assigned in the Telesploit email or readme.txt.
If connections to the Telesploit server fail verify direct connectivity to the relay.
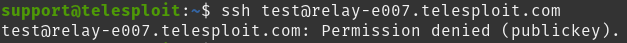
If the client is configured to use an SSH connection, then try directly accessing the SSH server on the relay. Logging in with the following command will fail, but it will validate that nothing is blocking access and that the relay is up.
Example: ssh test@relay-e007.telesploit.com
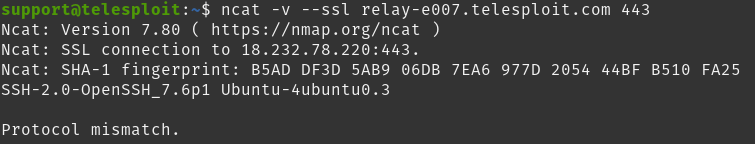
For TLS or proxy connections, try accessing the SSH server through the HA Proxy running on the relay using ncat. The output should be similar to the following if nothing is blocking access and the HA Proxy and SSH server are up.
Example: ncat -v –ssl relay-e007.telesploit.com 443
If these tests result in timeouts or no connections then verify that the outbound connections are not being blocked by a firewall or Intrusion Prevention System.
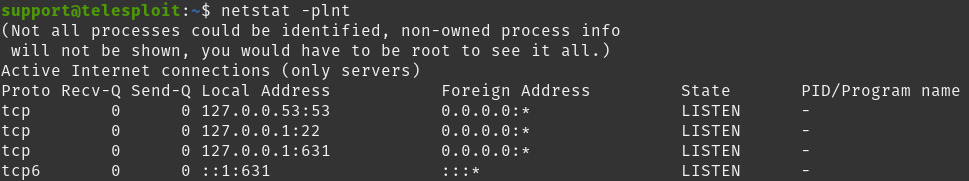
If the tests are successful then verify that the tunnels have been created by running netstat and reviewing the output.
If the tunnels have not been created then the output should look similar to the following depending on what services are running on the client system.
netstat -plnt
If the tunnels have been established then the output should look similar to the following, depending on what services are running on the client system. The established port numbers should match those provided in the Telesploit email or the readme.txt file for the deployment.
netstat -plnt | sort -k7
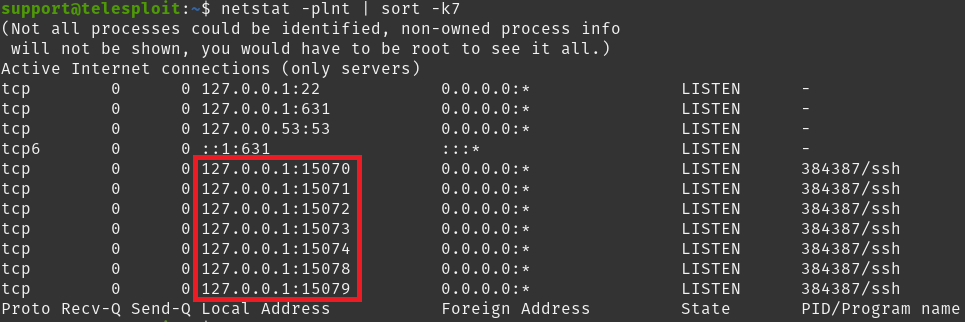
If the tunnels have not been established then re-run the script create_tunnels.sh. If the tunnels have been established then run the script kill_tunnels.sh followed by create_tunnels.sh to clear any potentially hung connections.
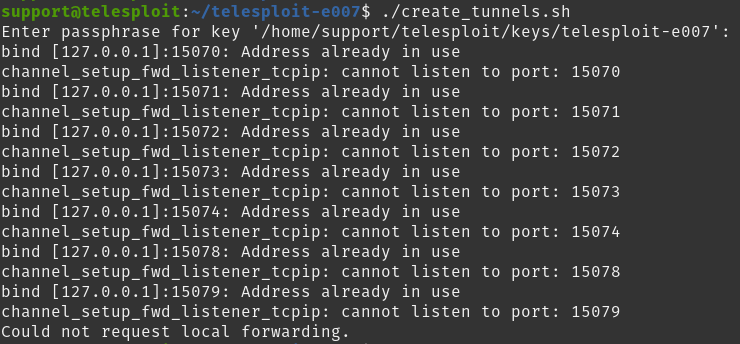
If an error similar to the following is received after running create_tunnels.sh then the tunnels have already been established.
If these steps are unsuccessful, then run the script kill_tunnels.sh followed by setup_client.sh before once again executing create_tunnels.sh.



