Once the Telesploit server has been provisioned, an email will be sent containing links to download the customized scripts for connecting to the assigned relay and server.
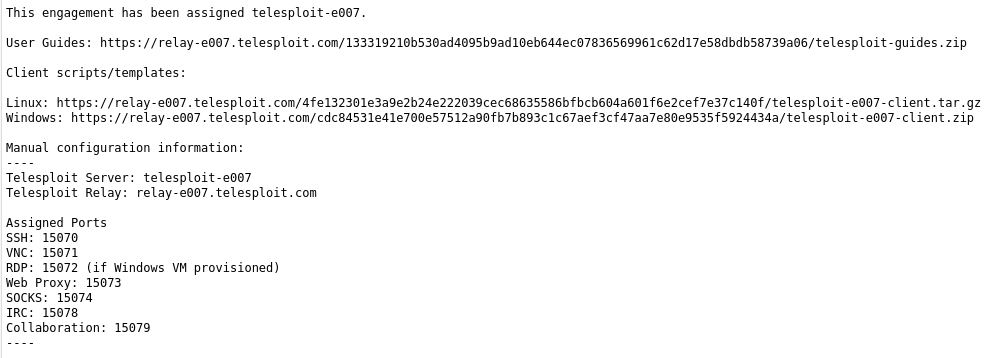
The examples in this documentation are for the Telesploit relay/server with the designation e007.
NOTE: Replace all URLs and port numbers in the documentation with those assigned in the Telesploit email.
Downloading and Extracting the Client #
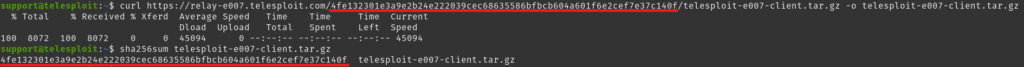
Download the archive file.
Example: Download Linux client with curl
curl https://relay-e007.telesploit.com/4fe132301e3a9e2b24e222039cec68635586bfbcb604a601f6e2cef7e37c140f/telesploit-e007-client.tar.gz -o telesploit-e007-client.tar.gz
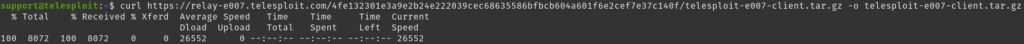
The integrity of the download may be validated by performing a sha256sum against the file. The value should match the subdirectory name in the URL.
If the checksum matches then create a client directory, extract the archive file, and change into the newly created directory.
Example: Extract Linux client configuration files
mkdir telesploit-e007 && tar -zxvf telesploit-e007-client.tar.gz -C ./telesploit-e007 && cd telesploit-e007
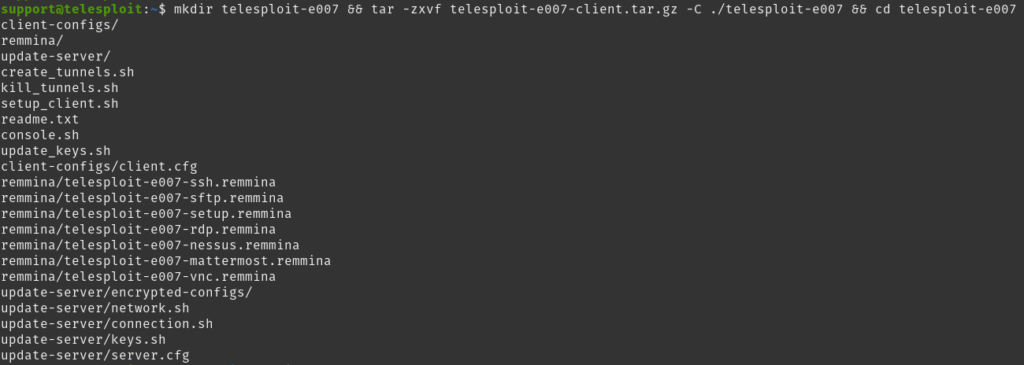
The readme.txt file contains the same server, relay, and port assignments as provided in the deployment email.
Example: Assigned Ports
- SSH: 15070
- VNC: 15071
- RDP: 15072 (if Windows virtual machine provisioned)
- Web Proxy: 15073
- SOCKS Proxy: 15074
- IRC: 15078
- Collaboration: 15079
NOTE: Replace all port numbers in the documentation with those assigned in the Telesploit email or readme.txt.
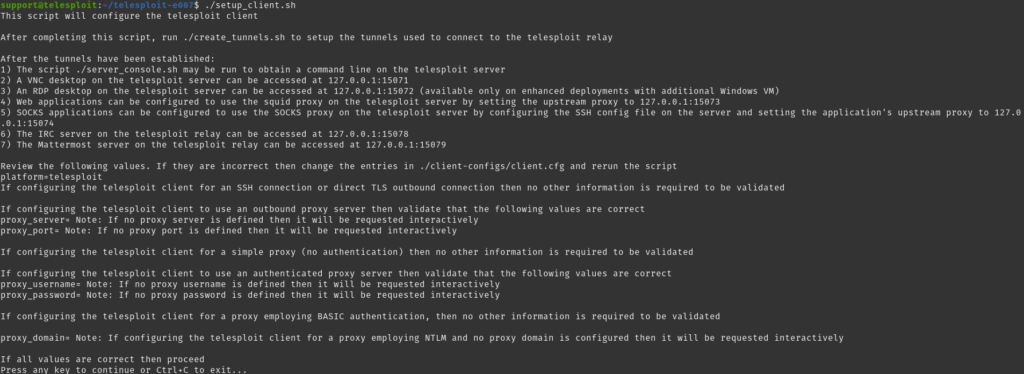
Configuring the Client #
Before connecting the first time, the client software must be configured by running the script setup_client.sh. If the environment allows outbound SSH then it is recommended to select that option. If the SSH connections will be tunneled through TLS then ncat (part of the nmap suite) will be required on the system. If the SSH connection will be tunneled through TLS and the environment requires using a proxy for outbound TLS connections then both ncat and proxytunnels are required. The proxy information will also need to be either entered in the configuration file client-configs/client.cfg or interactively from within the setup script.
./setup_client.sh
The script will prompt for the full path to the private key corresponding to the public key previously provided to Telesploit.

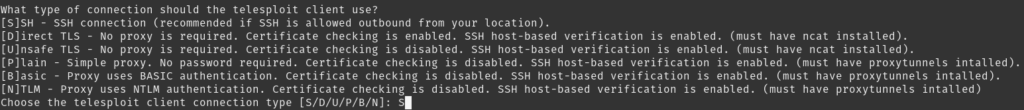
Choose the connection type. SSH is recommended. Direct (TLS) requires ncat to be installed, while all proxy connection types require both ncat and proxytunnels.
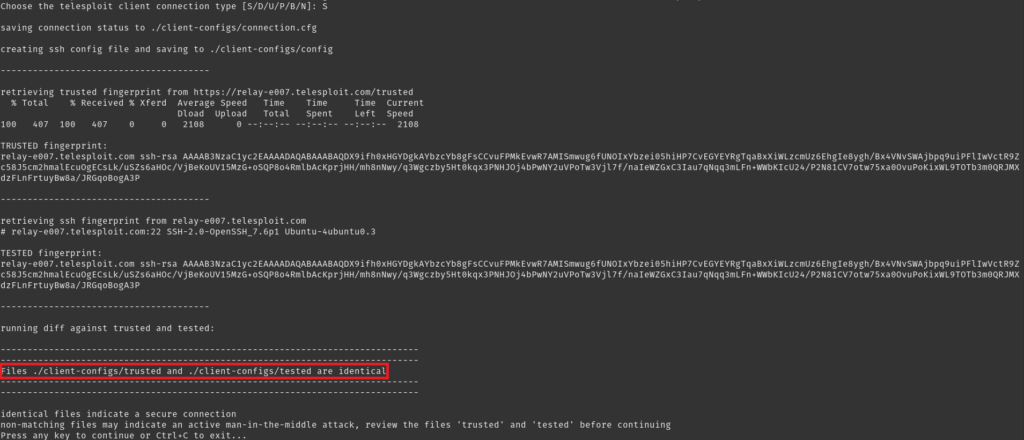
The script will then pull a file from the relay containing the SSH server’s known fingerprint and compare it to a locally generated version. Matching files indicate that an active Man-in-the-Middle attack is not being performed against the connection.
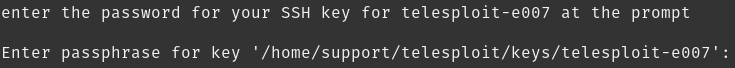
The script will then prompt for the password to the private key corresponding to the public key previously provided to Telesploit.
NOTE: If the script does not prompt for a password then verify the location and permissions (non-world readable) of the private key and that ncat is installed if connecting via TLS or ncat and proxytunnels if connecting via proxy and then re-run setup_client.sh.
The script will then terminate.
Establishing SSH Tunnels and Connecting to the Server #
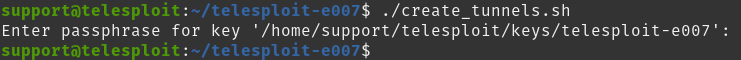
Once the client has been configured for the environment, verify that SSH tunnels to the relay can be created by running the script create_tunnels.sh. The script will prompt for the password to the SSH private key.
./create_tunnels.sh
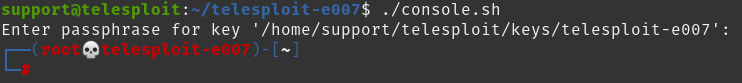
Once the tunnels have been established, verify connectivity by connecting to the Telesploit server using the script console.sh. The script will prompt for the password to the SSH private key. If everything has been configured properly a command prompt on the Telesploit server will be returned.
./console.sh
Disconnecting from the Server and Closing Tunnels #
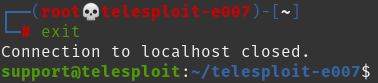
Typing ‘exit’ at the server command prompt will return control to the local system.
exit
When not performing testing, the tunnels can be closed by running the script kill_tunnels.sh.
./kill_tunnels.sh
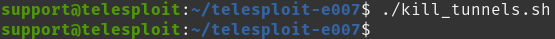
New connections to the Telesploit server do not require re-running the setup_client.sh script. Use the create_tunnels.sh script to bring the tunnels back up.



